Cloud Repatriation Explained: Costs, Risks & Benefits

Table of Contents
TLDR: Cloud repatriation is the process of moving workloads from public cloud back to on-premises or private infrastructure. It is a financially driven architectural correction. Gartner projects that by 2027, more than 50% of enterprises will revisit workload placement decisions made during cloud migration.
Cloud was sold as cheaper. For many workloads, it is not. A predictable database workload that costs $18,000 per month on AWS can run on owned hardware at $4,200 per month, amortized over three years. That math is driving a serious conversation in boardrooms. Cloud repatriation is the structured process of moving specific workloads back to on-premises or private infrastructure when the cloud cost model no longer fits the business model. This blog explains what cloud repatriation involves, what it costs, and how to decide if your organization is a candidate.
What Is Cloud Repatriation?
Cloud repatriation is the process of moving workloads back on-premises or to private infrastructure after a public cloud migration. Most organizations repatriate specific workloads to a steady-state, high-utilization, or compliance-sensitive environment, while keeping burst and cloud-native workloads in the public cloud.
It is a workload placement decision, not a technology rejection. The organizations doing it are pro-margin, not anti-cloud.
What It Replaces
Before cloud repatriation, IT teams had two choices: absorb rising cloud costs or rebuild infrastructure from scratch. Neither worked. It offers a third path, targeted workload migration for cases where on-premises vs cloud cost math favors owned infrastructure.
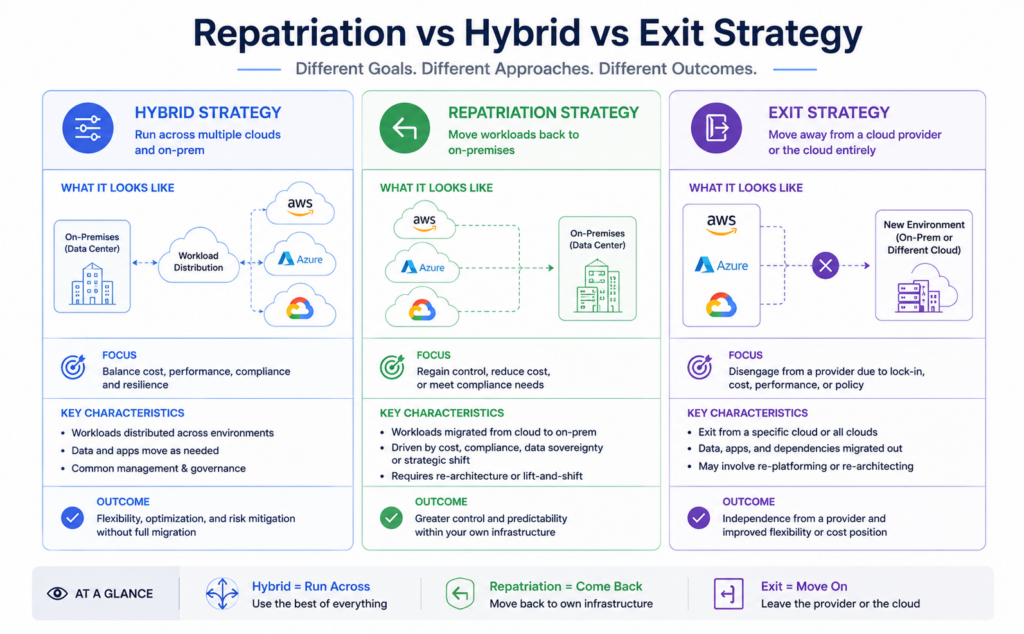
How It Differs from Adjacent Terms
Core Capabilities: What Cloud Repatriation Actually Involves
Workload Assessment and Dependency Mapping
Every cloud repatriation project starts with a workload inventory. Without it, teams discover mid-migration that applications share dependencies nobody mapped. A formal assessment produces a complete cloud repatriation roadmap with workload classification, dependency mapping, and cost modeling.
Assessment outputs:
- Utilization heatmap showing consistent vs. spiky compute demand.
- Dependency map identifying shared services and integration points.
- Repatriation candidate shortlist with projected savings per workload.
- Re-architecture requirements for cloud-native dependent workloads.
Infrastructure Provisioning On-Premises or Private Cloud
Moving workloads back on-premises requires hardware procurement before migration begins. Lead times run 4 to 12 weeks. This is the most underestimated timeline risk in any cloud repatriation program.
Data Migration and Integrity Validation
Egress fees make repatriation data migration more expensive than a standard cloud migration. Moving 50TB out of AWS at $0.09/GB costs $4,500 in egress alone. Every cloud exit strategy must include egress cost modeling before the first byte moves.
Validation steps every migration needs:
- Checksum verification at source and destination.
- Parallel run period with both environments live.
- Rollback plan with defined trigger criteria. Organizations spending over $500,000 annually on cloud with predictable base-load workloads owe themselves a formal repatriation asse
Application Re-Architecture (Where Required)
Applications built on AWS Lambda, Google Cloud Run, or Azure Cognitive Services create major migration challenges for cloud-native workloads. They require re-architecture before moving workloads back on-premises is feasible. The scoping question is whether the re-architecture cost is recoverable within the on-premises vs cloud cost savings window.
Operational Handover and Ongoing Management
Cloud repatriation does not end at cutover. Ongoing operations require internal skills or a managed services partner. Most organizations underestimate the operational overhead required to manage repatriated infrastructure at scale.
Why Businesses Move Workloads Back: 4 Operational Problems Solved
Uncontrolled Cloud Costs
The most common driver of cloud repatriation is cloud spend that outpaced the original business case. Reserved instance commitments run alongside on-demand charges for workloads that scaled past the commitment, and the gap compounds every quarter.
Cloud cost optimization inside the public cloud has limits. When 70%+ of spend covers steady-state compute, on-premises vs cloud cost analysis almost always favors repatriation.
For instance, A manufacturing company with 60 always-on database servers paid $2.1M annually on AWS RDS. After moving workloads back on-premises, total cost dropped to $680,000/year. The cloud exit strategy paid back in 22 months.
Data Sovereignty and Regulatory Compliance
GDPR, HIPAA, and PCI-DSS increasingly require demonstrable physical control over data. Some EU regulators now question whether third-party public cloud contracts satisfy data sovereignty requirements. Cloud repatriation to owned or collocated infrastructure removes that ambiguity entirely.
Performance and Latency Requirements
Public cloud cannot match on-premises infrastructure for sub-5ms latency. Financial trading, real-time manufacturing control, and high-frequency data processing all hit physical limits in shared cloud environments. Moving workloads back on-premises eliminates the unavoidable network hop between application and compute.
Workloads best suited for cloud repatriation:
- ERP systems with consistent 85%+ utilization.
- Relational databases with predictable query volumes.
- Rendering pipelines with continuous GPU demand.
- Latency-sensitive applications require a sub-5ms response.
Vendor Lock-In and Contract Risk
A cloud exit strategy becomes urgent when a provider's pricing changes at renewal. Organizations with 90%+ workload concentration on one provider have zero negotiating power. Cloud repatriation of even 30% of workloads creates enough leverage to renegotiate. The on-premises vs cloud cost comparison also reveals whether the original migration decision still holds.
Cloud Repatriation vs. Alternatives: Market Context
Cloud Repatriation vs. Cloud Optimization (FinOps)
FinOps should always come before cloud repatriation. Right-sizing instances and eliminating zombie resources can reduce cloud spend by 20 to 30% without moving workloads back on-premises. If a workload is spiky or under 70% utilization, optimization wins on TCO.
it wins when the workload is consistently high-utilization, and the FinOps savings have already been captured. If the bills are still growing after a FinOps pass, repatriation is the next conversation.
Cloud Repatriation vs. Multi-Cloud Redistribution
Multi-cloud redistribution moves workloads between public cloud providers to capture better pricing. It is a valid cloud exit strategy for provider-specific issues, but does not address the structural on-premises vs cloud cost problem for steady-state workloads. They solve different problems and should be evaluated separately.
Cloud Repatriation vs. Colocation (Colo)
Applications built on AWS Lambda, Google Cloud Run, or Azure Cognitive Services create major migration challenges for cloud-native workloads.
Colocation is a middle path. You own the hardware but colocate in a third-party data center, reducing the CapEx risk of moving workloads back on-premises while capturing most of the on-premises vs cloud cost savings.
| Option | CapEx | Control | Savings vs Cloud |
| Stay in the cloud | None | Low | 0% |
| Colocation | Medium | High | 40-55% |
| Full cloud repatriation | High | Full | 55-70% |
When NOT to Repatriate
Cloud repatriation is wrong for cloud-native serverless workloads, spiky seasonal compute, development and test environments, and applications requiring geographic distribution that your own infrastructure cannot serve.
Cloud Repatriation Costs: What to Budget

Workload Assessment and Strategy Phase
A formal assessment costs $5,000 to $25,000. It produces the workload classification, dependency map, and a TCO model comparing on-premises vs cloud cost over three years. This is the most important expense in the project. it determines whether moving workloads back on-premises is justified at all.
Infrastructure CapEx
On-premises hardware for 25 to 100 servers ranges from $250,000 to $700,000. Colocation reduces that by 30 to 40% by eliminating facility build costs. Hardware lead times of 4 to 12 weeks must be built into the cloud exit strategy timeline from day one.
Migration Execution and Engineering Labour
Engineering services run $40,000 to $180,000, depending on workload complexity. Total cloud repatriation project cost assessment, hardware, and engineering typically falls between $300,000 and $1M over a 3-year window.
Hidden and Ongoing Costs
Four costs every cloud repatriation budget misses:
- Egress fees at $0.09/GB out of the AWS or GCP model, this before migration starts
- Cloud cost optimization work is needed to clean up the remaining cloud footprint
- Internal staffing or managed services for ongoing on-premises operations
- Software licensing previously bundled in cloud pricing is now requiring separate procurement
Contract Models
Fixed-scope engagements give cost certainty for assessment and migration phases of a cloud exit strategy. Post-migration managed services run $5,000 to $20,000/month. Always confirm exit terms before signing. The last thing a repatriation project needs is a managed services lock-in replacing the cloud lock-in.
ROI and Business Impact of Cloud Repatriation
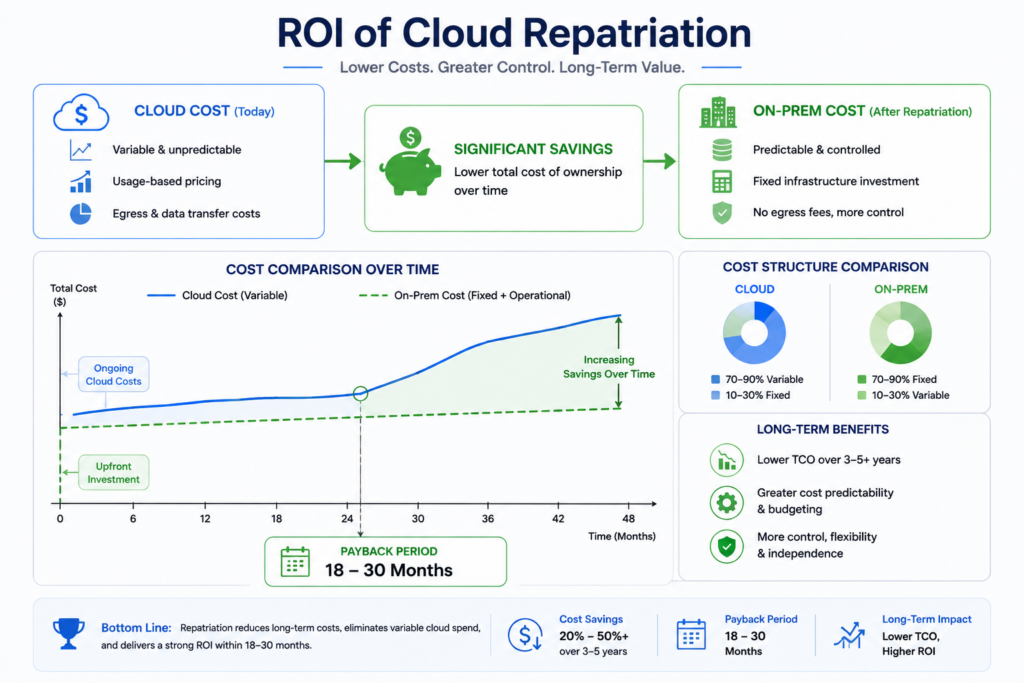
Direct Cloud Spend Reduction
Cloud repatriation converts variable cloud compute charges into fixed CapEx with a defined payback curve. For workloads at 85%+ utilization, on-premises vs cloud cost comparison delivers 55 to 70% infrastructure cost reduction over three years.
Time-to-Payback Analysis
Mid-market cloud repatriation environments reach payback in 18 to 30 months. A simple FinOps formula makes this concrete:
- Monthly cloud spend: $30,000
- Monthly on-premises amortized cost: $8,000
- Total project cost: $400,000
- Payback: 18 months
Moving workloads back on-premises turns a recurring operating expense into a one-time capital decision with a predictable return.
Compliance and Risk Mitigation Value
For regulated industries, cloud repatriation eliminates third-party audit overhead, DPA legal reviews, and annual compliance reporting costs that never appear in cloud bills but consume real budget.
Scalability and Burst Strategy
Cloud repatriation for base load, with public cloud retained for burst, is the operational model that works. Hybrid infrastructure delivers on-premises cost efficiency at steady state while keeping cloud elasticity for demand spikes.
Risks and Challenges of Cloud Repatriation
Underestimating Re-Architecture Complexity
The biggest technical risk in cloud repatriation is discovering mid-project that applications depend on cloud-native PaaS services with no on-premises equivalent.
Signs re-architecture risk is high:
- Application uses managed cloud databases with proprietary extensions.
- Workload relies on the cloud provider IAM for authentication.
- CI/CD pipelines are tightly coupled to cloud-native build services.
Every cloud exit strategy must include re-architecture scoping before hardware procurement begins.
Internal Skills Gap
Moving workloads back on-premises requires physical infrastructure management, on-premises network architecture, and storage administration. Most cloud-native engineering teams lack all three. Organizations that skip this gap assessment rebuild cloud dependency within 12 months.
Business Continuity During Migration
Every production workload in a cloud repatriation project needs a defined rollback trigger before cutover. Specific latency thresholds, error rates, or data integrity failures should automatically pause migration and restore cloud operation.
Contract Exit and Data Portability
Cloud provider contracts contain exit clauses that most teams never read before signing. Early termination fees, data portability SLAs, and support minimums all affect the true cost of a cloud exit strategy. Legal review of MSA terms is not optional before serving the exit notice.
Vendor Selection Checklist for Cloud Repatriation Partners
Before signing any contract for cloud repatriation services, confirm:
Technical Capability
- Does the vendor have certified expertise in both cloud and on-premises infrastructure for moving workloads back on-premises?
- Can they demonstrate completed cloud repatriation projects in your industry vertical?
- Do they perform re-architecture scoping before proposing hardware specifications?
Financial Transparency
- Does the engagement include a formal on-premises vs cloud cost TCO model before project kickoff?
- Is the cloud exit strategy scoped as fixed-price or time-and-materials?
- What are the post-migration managed services terms and exit clauses?
Operational Continuity
- What is their parallel-run methodology during cutover?
- How do they handle rollback if a workload fails post-migration?
- What does the operational handover model look like after cloud repatriation is complete?
A vendor that cannot produce a completed TCO model comparing on-premises vs cloud cost before project kickoff is not qualified to lead a repatriation program.
Top Cloud Repatriation Vendors: Company Profiles
Patoliya Infotech
A mid-market infrastructure partner delivering end-to-end cloud repatriation projects from workload assessment through operational handover, focused on engineering-led organizations that need production outcomes fast.
Key Features:
- Fixed-scope cloud repatriation assessment with TCO model comparing on-premises vs cloud cost delivered in two weeks.
- Re-architecture scoping for cloud-native workloads before hardware procurement begins.
- Managed services post-migration with a defined cloud exit strategy and handover terms.
Best For: Mid-market organizations spending $300,000 to $2M annually on cloud infrastructure with 30%+ steady-state workload concentration.
Client Review: 4.8/5
Rackspace Technology
A managed services provider with a dedicated repatriation practice supporting moving workloads back on-premises and colocation across enterprise environments.
Key Features:
- Managed colocation as a middle-path alternative to full repatriation.
- On-premises vs cloud cost analysis is integrated into every engagement.
- 24/7 post-migration operations with defined SLAs.
Best For: Enterprises that want managed infrastructure post-cloud repatriation without building internal operations capability.
Client Review: 4.5/5
Lumen Technologies
Overview: A network and infrastructure provider offering cloud repatriation services anchored in its own colocation and private network infrastructure across North America and Europe.
Key Features:
- Private network connectivity that eliminates public internet dependency post-cloud repatriation.
- Colocation options that reduce CapEx versus a full on-premises build.
- Cloud exit strategy planning with contract review support.
Best For: Organizations with high-bandwidth, latency-sensitive workloads where network performance is the primary repatriation driver.
Client Review: 4.4/5
Faction
A private cloud and colocation provider specializing in cloud repatriation for regulated industries, including healthcare, financial services, and government.
Key Features:
- Compliance-ready infrastructure for HIPAA, PCI-DSS, and FedRAMP, moving workloads back on-premises.
- Multi-site colocation for cloud exit strategy with built-in redundancy.
- On-premises vs cloud cost modeling with compliance overhead factored in.
Best For: Regulated industry organizations where compliance is the primary cloud repatriation driver.
Client Review: 4.5/5
11:11 Systems (formerly iland)
A managed cloud and infrastructure provider offering hybrid infrastructure services for organizations executing partial repatriation while retaining burst capacity in public cloud.
Key Features:
- Hybrid infrastructure design connecting repatriated workloads with retained cloud burst capacity.
- Disaster recovery integration for moving workloads back on-premises without losing cloud-based DR.
- Unified management layer across on-premises and cloud post-cloud repatriation.
Best For: Organizations executing a partial cloud exit strategy that retains public cloud for burst and DR while repatriating base load.
Client Review: 4.4/5
Why Patoliya Infotech for Cloud Repatriation
We deliver cloud repatriation projects to production in 3 to 5 months. Most organizations budget 9 to 12 months managing it internally.
Three things that make our work different:
- TCO-first model. Every engagement starts with a formal on-premises vs cloud cost analysis. If cloud repatriation does not pencil out over three years, they say so before you spend anything.
- Re-architecture scoping before hardware procurement. Applications with cloud-native dependencies are scoped for re-architecture cost before a single server is ordered. This is the most common reason moving workloads back on-premises projects run over budget.
- Defined handover terms. Every cloud exit strategy engagement includes clear operational handover with fixed-cost managed services and contract exit terms that do not recreate the dependency you just escaped.
Turn predictable workloads into predictable savings. Let's run the numbers together.
Conclusion:
Cloud repatriation has moved from a niche decision to a mainstream infrastructure strategy. Gartner and IDC both project sustained growth in on-premises and private cloud investment through 2027. Base the decision on workload utilization patterns, Every cloud exit strategy must include egress cost modeling before the first byte moves.compliance requirements, and a clear total cost of ownership model.
Organizations spending over $500,000 annually on cloud with predictable base-load workloads owe themselves a formal repatriation assessment before their next renewal cycle. Get a scoped cloud exit strategy estimate from Patoliya Infotech before that conversation starts.