DevSecOps Explained: How to Shift Security Left in Your Software Delivery Pipeline

Table of Contents
TLDR: DevSecOps integrates security testing directly into CI/CD pipelines instead of treating it as a final gate before release. Security handled after deployment is already a risk multiplier. When code is reviewed only at the end, issues are discovered too late, when the cost and impact are higher.
Security reviews after deployment are not real reviews. They signal gaps in the process. A structured DevSecOps program shifts security into every stage, reducing exposure, improving control, and preventing issues before they reach production.
It is an operating model that treats security as a shared engineering responsibility, not a compliance handoff. Most teams that struggle with it are not missing tools; they are missing a DevSecOps pipeline architecture that makes security enforcement automatic. This guide covers what it costs, how it works, and which vendors actually deliver.
What Is DevSecOps?
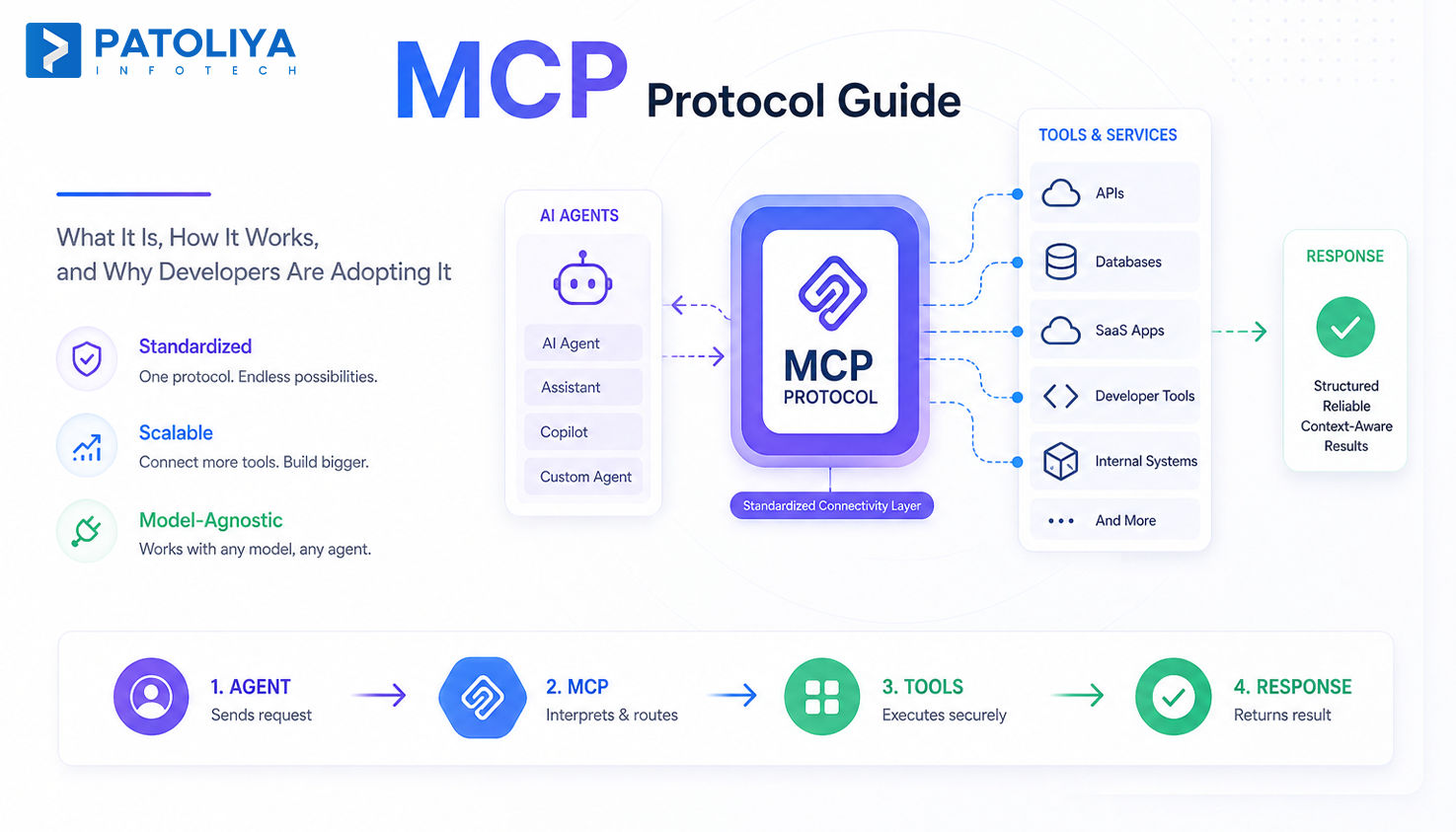
DevSecOps embeds automated security controls at every delivery stage so vulnerabilities are caught before they become production incidents.
The word "embeds" matters here. Every commit triggers security checks defined by security as code policies. Developers get feedback in the same environment where they write code.
What DevSecOps Replaces in Traditional Application Security
The model it replaces is security at the gate, and an AppSec team reviewing code right before release. That creates a backlog and finds vulnerabilities too late. IBM estimates that fixing a vulnerability in testing costs 15x more than fixing it at the code stage.
DevSecOps vs. DevOps vs. AppSec: The Precise Difference
DevOps optimizes for speed. AppSec works in isolation after code is written. The practice merges both security runs automatically in the pipeline, and developers' own remediation.
Where DevSecOps Lives in the SDLC
It touches every phase: SAST DAST integration at code commit, dependency scanning at build, container security scanning during packaging, and policy enforcement at deployment.
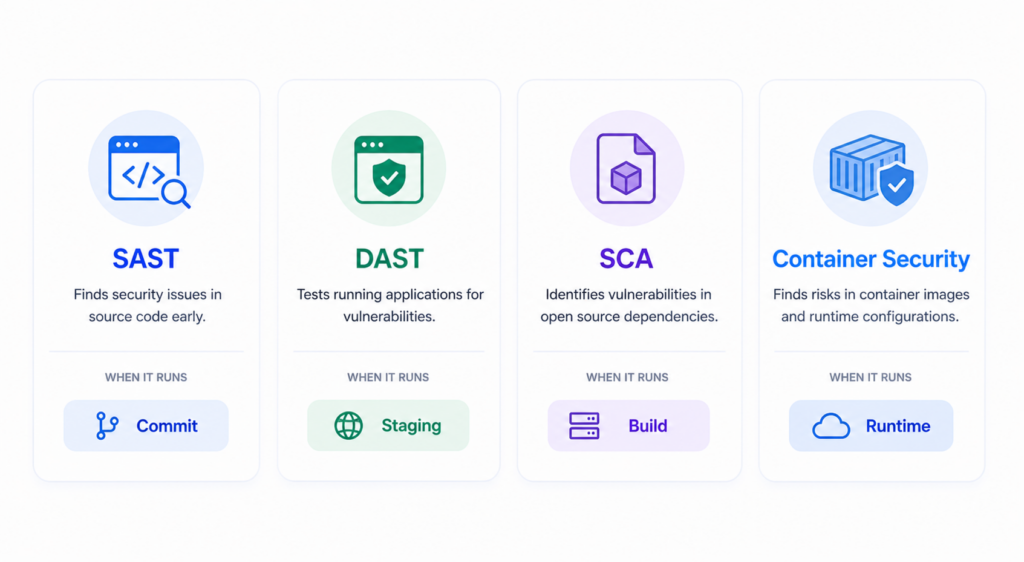
Static Application Security Testing (SAST)
SAST scans source code without executing it, finding injection flaws and hardcoded credentials. In a mature build, tools like Semgrep and SonarQube run in under two minutes. In a mature pipeline, a failing SAST gate blocks a merge request the same way a failing unit test does. Target false positive rate: under 15%.
Dynamic Application Security Testing (DAST)
DAST tests running applications by simulating outside attacks. It catches runtime vulnerabilities that static analysis cannot see. Tools here run best in staging on a nightly schedule, not every commit, where latency creates friction.
Software Composition Analysis (SCA) and Supply Chain Security
SCA scans open source dependencies for known CVEs. The 2024 Sonatype report found 245,000 malicious packages published to open source repositories in 2023. DevSecOps tools running SCA inside the pipeline block builds when a dependency carries a critical CVE.
Container Security Scanning and Infrastructure as Code (IaC) Security
DevSecOps tools like Trivy and Aqua handle container security scanning at image build time. Checkov scans infrastructure configurations before they reach production. The tools here prevent the most common cloud breach vector: misconfigured permissions.
Secrets Management and Policy Enforcement
HashiCorp Vault integrates at the pipeline level and blocks deployments with exposed credentials. Security as code policies run here automatically.
The 4 Operational Problems DevSecOps Solves
Problem 1: Security Bottlenecks Delaying Release Cycles
When the security team is a gate, delivery slows. The DevSecOps pipeline moves security checks earlier so development and security run in parallel, not in sequence. Every stage of the pipeline is a checkpoint, not a bottleneck. Teams that implement shift-left security properly report no increase in release cycle time.
Problem 2: Undetected Vulnerabilities in Production
Code reaching production without automated scanning carries vulnerabilities that auditors find months later. By then, the fix requires patching production and retesting. A continuously running pipeline with SAST, DAST, and SCA catches vulnerabilities before code ships; that is, the DevSecOps pipeline is functioning as designed.
Problem 3: Compliance Gaps Creating Audit Risk
SOC 2, PCI-DSS, HIPAA, and ISO 27001 all require evidence of security controls. Manual processes generate documentation that is incomplete and hard to reproduce under audit. Security as code policies map compliance controls directly to pipeline checks. Compliance automation built into the pipeline generates timestamped evidence automatically.
Problem 4: Software Supply Chain Vulnerabilities
SolarWinds and Log4Shell proved that the biggest attack surface is not your code, it is the dependencies your code pulls in. Software supply chain security via SCA in the pipeline is the only scalable answer.
DevSecOps vs. Traditional AppSec vs. DevOps-Only: Market Comparison
The Maturity Spectrum: Ad-Hoc → DevOps → DevSecOps → SecDevOps
Most engineering organizations sit on a four-stage maturity curve: ad hoc security, DevOps without security automation, DevSecOps with automated gates, and SecDevOps with embedded security architects. Most teams that claim this maturity are actually at stage two.
Comparison Matrix - DevSecOps vs. Traditional AppSec vs. DevOps
| Dimension | Traditional AppSec | DevOps Only | DevSecOps |
| Security timing | After development | None automated | Every pipeline stage |
| Who owns fixes | Security team | Development team | Development team with guidance |
| Compliance evidence | Manual | None | Automated artifacts |
| Velocity impact | High, blocks releases | Zero | Low when tuned |
| Tools used | Point tools only | None | Integrated toolchain |
Buy vs. Build vs. Partner: The Three DevSecOps Implementation Paths
Building a DevSecOps pipeline in-house works for teams with dedicated security engineers. Commercial platforms bundle most of what a pipeline needs. Managed partners handle the build for teams without internal security capacity. Security as code policy definitions live alongside application code in the same repository.
DevSecOps Implementation Cost: What You'll Actually Pay
Cost Tier 1: Open-Source Toolchain (DIY)
A toolchain built on open source DevSecOps tools like Semgrep, OWASP ZAP, Trivy, Checkov, and HashiCorp Vault costs $15,000 to $45,000 in implementation labor. Ongoing maintenance requires at least one engineer who owns the toolchain. The real cost is tuning: false positive suppression takes significant ongoing time.
Cost Tier 2: Commercial Platform
GitLab Ultimate, Snyk, and Veracode bundle SAST, DAST, SCA, and container security scanning in a single platform. For a 50-developer team, commercial tool licensing runs $60,000 to $150,000 per year. Most mid-market teams recover platform costs within 18 months through reduced remediation spend.
Cost Tier 3: Managed DevSecOps Service
A managed implementation where a partner builds and tunes the full pipeline runs $40,000 to $200,000, depending on stack complexity. Ongoing managed retainers run $8,000 to $25,000 per month.
Contract Models and Negotiation Considerations
Fixed scope contracts work for Tier 1 and Tier 2 builds. Managed service retainers almost always run on time and materials. Budget a 15% contingency. The biggest cost surprises come from legacy CI/CD platforms that need custom connectors for security tooling.
ROI and Business Impact of DevSecOps
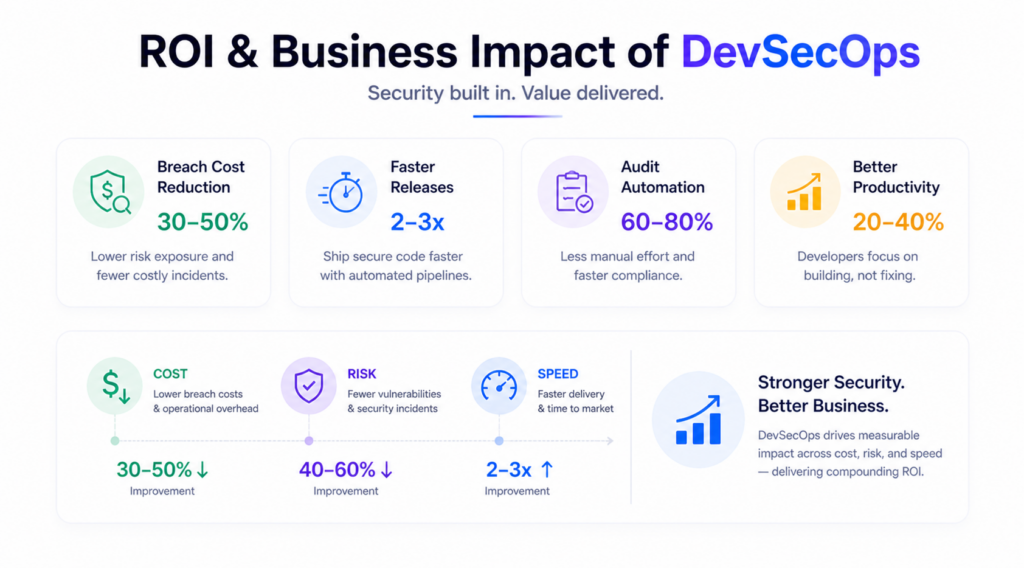
Breach Cost Avoidance
- The ROI is driven by reducing breach impact through early detection and prevention.
- The IBM 2024 Cost of a Data Breach Report estimates the average breach at $4.88 million.
- Organizations with a mature DevSecOps pipeline reported $1.68 million lower breach costs per incident.
- Security integrated into development reduces exposure before vulnerabilities reach production.
Release Velocity and Developer Productivity
- A well-implemented pipeline adds minimal overhead to build time, typically under 10 minutes.
- Developers identify and fix issues earlier, when context is still fresh.
- As Chris Romeo notes, security must align with developer workflows to avoid bypassing controls.
- Faster remediation improves release cycles without compromising security standards.
Compliance Cost Reduction
- It embeds compliance directly into the pipeline through security as code.
- Audit preparation has reduced from weeks to days due to automated evidence generation.
- Eliminates manual tracking and reduces dependency on security teams for compliance reporting.
Scalability Economics
- A pipeline's scale without proportional increases in security headcount.
- Every new service inherits predefined security policies automatically.
- Unlike traditional AppSec, no manual review is required for each deployment.
Risks and Challenges in DevSecOps Implementation
Tool Sprawl and Alert Fatigue
- Deploying too many DevSecOps tools at once creates fragmented visibility across dashboards.
- Multiple alert sources without clear ownership lead to ignored or dismissed alerts.
- Best practice: start with core tools like SAST, SCA, and secrets scanning.
- Expand only after tuning alert quality and establishing triage workflows.
False Positive Rate and Developer Friction
- High false positives reduce trust in pipelines and slow adoption.
- A SAST tool generating excessive alerts (e.g., 200+ weekly) gets ignored quickly.
- Target a false positive rate below 15% to maintain developer engagement.
- Pre-configured rule sets from experienced partners help reduce noise and improve accuracy.
Skills Gap and Security Champion Enablement
- Lack of in-house expertise slows its implementation and adoption.
- Security Champions, one trained engineer per team, distribute security ownership.
- This model scales security as code without creating a central AppSec bottleneck.
- Enables faster issue resolution within development teams.
IP and Code Exposure in Third-Party Engagements
- DevSecOps tools integrated into CI/CD pipelines have access to full codebases.
- Clearly define IP ownership, NDA terms, and data handling policies before engagement.
- Ensure vendors follow strict access control and security compliance standards.
DevSecOps Vendor Selection Checklist: 10 Decision Criteria
Checklist Item 1 - CI/CD Platform Compatibility
- Ensure tools integrate natively with your CI/CD platform without custom setup.
Checklist Item 2 - SAST, DAST, SCA Tool Coverage
- Verify full coverage across SAST, DAST, and SCA. A DevSecOps pipeline with only one layer is incomplete.
Checklist Item 3 - Container and Cloud Native Security Capability
- Confirm container and cloud workload scanning at your required scale within the tools.
Checklist Item 4 - Compliance Framework Coverage
- Check if security as code policies map to SOC 2, PCI DSS, HIPAA, or ISO 27001 frameworks.
Checklist Item 5 - False Positive Rate Benchmarks
- Ask for documented benchmarks. The tools should maintain false positives under 15%.
Checklist Item 6 - Mean Time to Notify on Critical CVEs
- Confirm MTTN for critical CVEs. A production pipeline should notify within the same day.
Checklist Item 7 - Developer Experience and IDE Integration
- Ensure tools surface findings directly in the IDE, not only in CI logs.
Checklist Item 8 - Audit Ready Reporting and Evidence Packaging
- Verify automated reporting and audit evidence generation through security as code workflows.
Checklist Item 9 - Pricing Transparency and Licensing Model
- Avoid per scan or per seat pricing models. Choose scalable tools and pricing structures.
Checklist Item 10 - Reference Clients in Your Industry Vertical
- Request long-term client references and confirm post-deployment support for tools.
Top DevSecOps Vendors and Partners in 2026
The market splits into platform providers, point tool specialists, and implementation partners.

Patoliya Infotech
Patoliya Infotech designs and implements DevSecOps pipelines for mid-market and enterprise clients across fintech, healthcare, and SaaS sectors, where strict compliance requirements demand security as code, audit-ready controls, and tightly integrated tools.
Key capabilities:
- Complete pipeline delivery using purpose-built tools: SAST, DAST, SCA, container security scanning, secrets management, and compliance automation.
- Security as code policy authoring using tools mapped to client compliance frameworks.
- The Embedded Security Champion model is included in every engagement.
Best for: Organizations needing a ready for production program with compliance coverage and no internal security engineering capacity.
Client review: 4.8/5
Snyk
Snyk leads in SCA with tools built around the developer experience.
Key capabilities:
- Best-in-class SCA for software supply chain security.
- IDE and PR-level DevSecOps tools integration.
- Container and IaC scanning in one platform.
Best for: Developer teams wanting security feedback in the IDE, not just in CI.
Client review: 4.7/5
Veracode
Veracode is an enterprise SAST and DAST platform with the strongest security as code compliance reporting in this space.
Key capabilities:
- Policy-based DevSecOps pipeline enforcement is ready for audit reporting.
- Strong PCI-DSS and HIPAA evidence generation via security as code policies stored as versioned configurations.
- DevSecOps tools compatibility with Jenkins, GitHub Actions, and Azure DevOps.
Best for: Regulated enterprises needing auditable compliance evidence annually.
Client review: 4.5/5
GitLab DevSecOps Platform
GitLab Ultimate bundles secure CI/CD and DevSecOps tools in one platform, eliminating integration overhead.
Key capabilities:
- Native SAST, DAST, SCA, and container security scanning in one UI.
- Pipeline policies are managed as security as code in the same repository as the application code.
Best for: Teams already on GitLab wanting security automation without added tools.
Client review: 4.6/5
Aqua Security
Aqua specializes in container and cloud native security with DevSecOps tools that go deeper than general platforms on Kubernetes risk.
Key capabilities:
- Deep container security scanning for Kubernetes environments.
- Runtime protection is included alongside scan results.
Best for: Kubernetes environments where container security is the primary risk surface.
Client review: 4.7/5
Why Patoliya Infotech for DevSecOps Implementation
We stay after delivery and have built DevSecOps pipelines on GitHub Actions, GitLab CI, Jenkins, and Azure DevOps with pre-configured rule sets.
Every pipeline they deliver maps security as code policies to compliance frameworks. Every security as code asset lives in version control. Auditors get evidence artifacts, not spreadsheets.
- Full DevSecOps tools stack: SAST, DAST, SCA, secrets management, container security scanning, IaC scanning, and SIEM integration, all in one engagement with a single point of accountability.
- Fixed scope contracts, no per-scan pricing surprises.
- Security Champion training for one engineer per team is included by default.
Ready to move from manual AppSec to a production DevSecOps program? Let's talk.
Conclusion
It is an architecture decision, not just a product purchase. Organizations that succeed embed security as code into the DevSecOps pipeline from the start, while designing for a strong developer experience. This ensures security is enforced without slowing delivery.
The DevSecOps tools ecosystem is mature, and capable vendors are available. What matters is how early and effectively security is integrated. Treating security as a post-deployment step creates risk, delays fixes, and increases costs. In modern systems, it must be built into the pipeline, not added after release.
If you are planning to implement or optimize your DevSecOps pipeline, connect with the team to get a scoped, security-first approach aligned with your architecture and compliance needs.
FAQs:
How much does DevSecOps implementation cost?
What is the difference between DevSecOps and DevOps?
How long does it take to implement a DevSecOps pipeline?
What tools are required for a complete DevSecOps pipeline?
What compliance frameworks does DevSecOps support?
What are the biggest risks in DevSecOps implementation?
(1) Tool sprawl generating unmanageable alert volumes, mitigated by starting with a maximum of three tools;
(2) High SAST false positive rates causing developer abandonment, with a target of under 15%.
(3) Skills gaps, addressed through Security Champion programs and embedded training within the pipeline.