
Table of Contents
The primary function of healthcare software security is patient safety, not data loss. A diabetic's health and finances suffer when they use mhealth apps, and there is a data breach.
Digital health solutions like telehealth apps, AI-powered diagnostics, and IoMT equipment are being adopted by the healthcare industry. This proves that patient safety happens online and also in hospitals.
The benefits of technology bring new challenges. This includes weak authentication, insecure APIs for social engineering, and unpatched devices. These risks have made cybersecurity in healthcare a clinical requirement.
Multi-factor authentication (MFA), data encryption (AES-256, TLS), and other security measures can all help decrease the risk. This is important in protecting Protected Health Information (PHI) against ransomware in the medical field, as well as other new dangers.
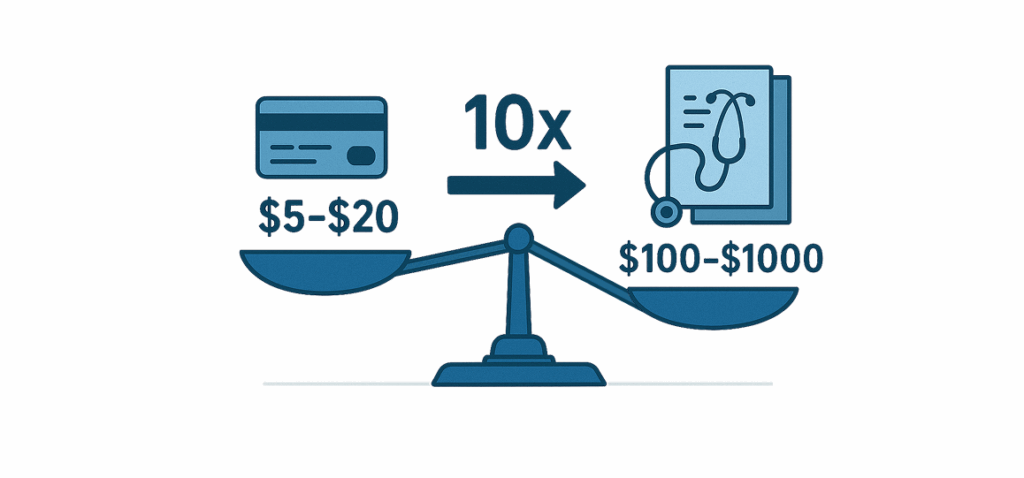
On the black market, protected health information (PHI) is market value up to ten times as much as credit card data.
The IBM Security 2024 Cost of a Data Breach Report states that healthcare data breaches cost $10.93 million per incident. As to the survey, about 63% of firms lack AI governance strategies to control AI and prevent scenarios. (Src)
The nature of the threat is dominated by financially motivated attacks, such as ransomware in healthcare. The majority of healthcare breaches are motivated by the need for money. This is why healthcare software security is so important.
| What is the Challenge? | What Does It Mean? | Example |
| Data Breaches | Hackers steal valuable patient information like medical records and personal details to sell on the black market. | The 2024 Change Healthcare cyberattack exposed data from over 190 million Americans. The hack started with a partner company, but it affected millions of people. |
| Weak Authentication Policies | Hackers can easily gain access to many apps because they allow users to use simple passwords or lack a second security check. | A doctor used the same simple password for multiple apps. When his password was stolen from one site, hackers used it to get into his hospital account. |
| Issues with Data Transmission | Data is most at risk when it is moving from one place to another. If it is not protected with a special security lock, anyone can read it. | Imagine sending your medical records on a postcard. Everyone can read it. That is what happens when data is sent without encryption. |
| Insecure Data Storage | Even when data is not being used, it still needs to be protected. Hackers can easily steal it if it is not encrypted while being stored on a server. | A major health system made a mistake in how they set up their cloud storage, and millions of patient records were accidentally left public on the internet. Secure data storage is the most important step for healthcare software security. |
| Third-party Components and APIs | Most apps are built using tools and services from other companies. If one of those tools has a weakness, hackers can use it to break into the main app. | A new telehealth app used a common software tool that had a hidden weakness. Hackers found it and used that one flaw to get into the data of thousands of patients. |
| Outdated Software Systems | Many hospitals use very old software that is no longer updated or protected by its creators. These systems are easy for hackers to get into. | In 2017, hospitals still running an outdated version of Windows were targeted by the WannaCry attack. There was a huge issue because the software was so outdated that it could not be fixed.. |
| Lack of Encryption | This is the core problem behind data transmission and storage issues. It means data is not being protected at all. Lack of encryption leads to loss of data in healthcare software security. | Data is not being protected with the two types of security locks: one for when it is moving, and one for when it is sitting still. |
| Social Engineering Attacks | The weakest link happens to be people. Hackers sometimes appear as people they know in order to trick staff into revealing personal information. | A fake email that appeared authentic was sent to an employee. They unintentionally gave hackers access to the hospital's whole computer system when they clicked on a link. |
| Not Enough Security Testing | A business is just hoping for the best if it does not regularly inspect its apps for flaws. Hackers are constantly searching for weaknesses, and if there are any, they will find them. | Without a full security check, a new app was released. A security specialist later discovered a significant vulnerability that might have given a hacker access to the app and allowed them to steal patient data. |
| Compliance Violations | Not following strict security rules like HIPAA means a company is likely cutting corners, which makes them a target for hackers. | A major hospital was fined heavily because it did not have the proper security in place to protect patient data, which was a violation of federal law. |
| Human Error & Insider Threats | Employees can be a risk, either by making a simple mistake or by intentionally stealing information for personal gain. | An annoyed employee downloaded and sold patient information from a hospital database, which he was able to access with his normal login. |
| Medical Device (IoMT) Security | Smart medical devices like insulin pumps and heart monitors are often made without strong security. Many have a permanent password that can not be changed. | The FDA has warned about devices that have security flaws. In some cases, hackers could change the settings of a device, putting a patient's life in danger. |
| Cloud Security in Healthcare | More healthcare data is stored in the cloud for healthcare software security. While cloud companies are secure, if a hospital sets up its account incorrectly, the data can be left wide open. | A major health system made a mistake in how it set up its cloud storage. As a result, millions of patient records were accidentally left public on the internet for anyone to see. |
| Technical & Foundational Security | Adopt Strong Encryption When storing data on a server, use AES-256, and when sending data over a network, use TLS. This breaks down data, rendering it illegible for hackers who intercept it. Implement Strong Authentication This requires multi-factor authentication. This introduces a Multi-Factor Authentication (MFA) step for all users. Use role-based access control (RBAC) to ensure that employees only have access to the necessary data. Conduct Regular Security Audits Perform regular security audits. Security is a continuous process. Conduct regular vulnerability testing. This helps to find and correct software issues. Also, perform complete security audits. This validates system compliance and security. This proactive strategy helps to identify problems before hackers do. |
| Organizational & Human Security | Secure Third-Party Integrations Before using any third-party vendor or API, conduct a complete security evaluation. This makes sure that partners satisfy your security criteria and decreases the chance of a supply chain cyberattack. Minimize Data Adopt a data minimization policy, collecting and storing only necessary patient information. If you do not have the data, it cannot be taken, effectively lowering your overall risk in healthcare software security. Prioritize User Education The human aspect is a significant danger factor. Provide regular, required security awareness training and realistic phishing simulations to teach employees how to recognize and report attacks, making them a strong line of defense. |
| Strategies for the Future | Automate Updates & Timeouts Create a regular patching schedule. This automatically upgrades software and fixes vulnerabilities. Also, use automatic session timeouts. This locks users out after inactivity to prevent unwanted access. Embrace AI with Caution Use AI-powered solutions to detect threats in real time, search for patterns, and identify unusual user activity. This helps security teams to detect and prevent complicated threats that standard technologies may miss in healthcare software security. Patient-Centered Security Empower patients by providing simple tools for managing their data access and preferences. Provide openness about how their data is handled and stored, and use consent-based mechanisms. |
| Holistic Approach | Incident Response Plan Always plan for the future. It is not necessary to prepare until the last minute; instead, you should have a backup plan. This aids in recovering and gaining control of the situation. |
Firms require specialists with advanced knowledge of technology linked to software security and cybersecurity. Trust Patoliya Infotech's 15+ years of experience in technology for the healthcare sector.
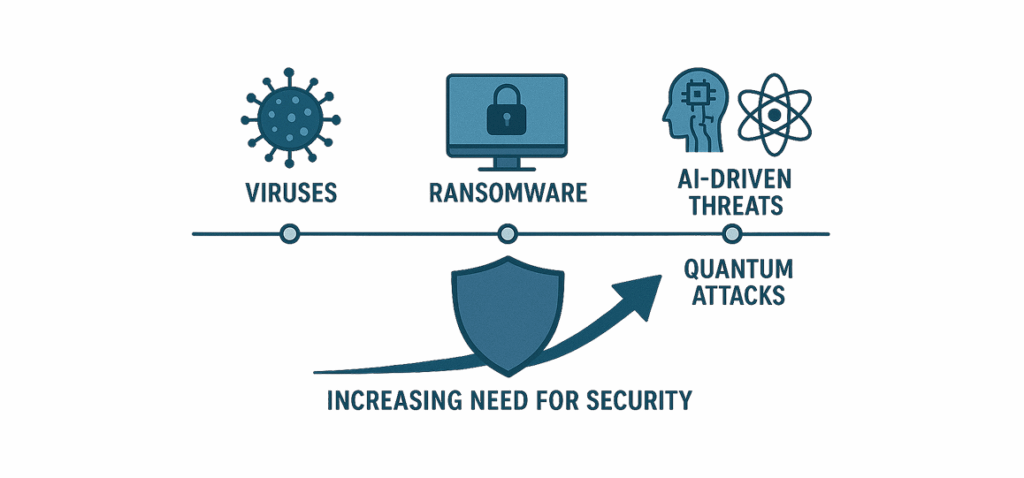
The future of quantum algorithms requires advanced security standards. Our current security methods can’t be useful for healthcare data protection. This will demand the adoption of post-quantum cryptography to safeguard Protected Health Information (PHI).
Governments are passing stricter laws to protect patient privacy. The EU AI Act and new HIPAA compliance regulations are becoming stricter. If a corporation fails to follow these standards, it could face fines and lose the trust of its customers forever.
It is a system that prevents sensitive information, such as a patient's medical records, from being forwarded to an illegal place, such as a personal email account.
This system records who has viewed a patient's data. It does not store the data directly, but it does create a permanent log that cannot be changed. This makes sure that medical records are authentic and have not been edited.
This method replaces sensitive patient data with a random, useless piece of information known as a token. The true data is held in a secure vault.
These solutions help companies comply with all regulations without requiring much manual labor. They verify everything automatically to make sure it is up to code for software security.
The impact of a healthcare software security breach reaches far beyond the cost. They cause direct harm to patient well-being and human life.
Ransomware is capable of locking hospital systems. This affects medical care, resulting in terrible outcomes. This is solved with technical solutions such as data loss prevention (DLP), Zero-Trust architecture, and many others. Detailed user training and incident response planning are also important when implementing healthcare software security.
Caring for patients is both our professional and ethical responsibility. Cybersecurity has to advance with technology. We have to treat cybersecurity with the same care as medical care.
All healthcare security starts with secure software and technologies. At Patoliya Infotech, we understand your technical requirements for healthcare security. Call us now.